It is no secret that Motorola CPS software does not like to run on modern operating systems. I still have a number of UHF Motorola MTS2000 handhelds which once given new batteries have proven themselves useful time and time again.
However my trusty old Windows XP laptop, with a real serial port fried its motherboard recently never to boot again. My immediate thought was “yikes what do I use now to program these Motorola radios” ?
So rather than go looking for further ancient hardware I started experimenting if Motorola CPS would run on a Windows 10 64-bit platform. I’ll spare you the gory details, but not amount of compatibility mode twiddling or research would result in a working system. There is something fundamental in the RS232 32-bit sub-system within the CPS software that prevents this from ever working. I could not get the CPS software to “read device” instead receiving a timeout. Grrrr….
So the only alternative was to experiment with an older version of Windows in a virtual machine and passing through a serial port. I remember when Windows 7 was first released Microsoft released a version of Windows XP that would run within Microsoft Virtual PC. The Motorola CPS software is from around the same time, so it was an ideal candidate to try. Turns out this was easier than I expected.
Setup Windows XP Virtual Machine
I found the following setup guide very useful from Help Desk Geek website (click). The download link from the Microsoft site has disappeared, but the alternative link from the CNET site was working at the time of this post.
I followed this guide closely, there are a few steps you needed to pay attention too but otherwise this went smoothly. I’m currently using a Windows 10 host and the only trouble I had was with the mouse, where I could not control the mouse within the Guest correctly, but you can temporarily disable the VirtualBox “mouse integration” feature to get around this until the VirtualBox Guest Additions are installed. Once the Guest additions were installed, everything worked as expected.
Activating Windows XP in 2022
The next challenge is since Windows XP support ended there is no way to “activate” this vanilla of windows any more which is right painful. One work around is to snapshot the VM and rollback each time you wish to use it, I wasn’t a fan. So thankfully the “Adventures in Nostalgia” YouTube channel had a video that shows how a regedit method to work around this problem, don’t forget to leave a like.
Serial Port Pass Through
Now I’m lucky that my Gen-3 I7 desktop machine has a real serial port on the motherboard. This was one of the very last Intel made motherboards with the legacy IO chipset, so not only do I have a serial port it has a parallel port too.
To allow Windows XP access to the host serial port, one just needs to configure the hardware pass through. Within the VirtualBox settings there is a separate “Serial Port” tab that simply requires mapping between the guest and host systems.
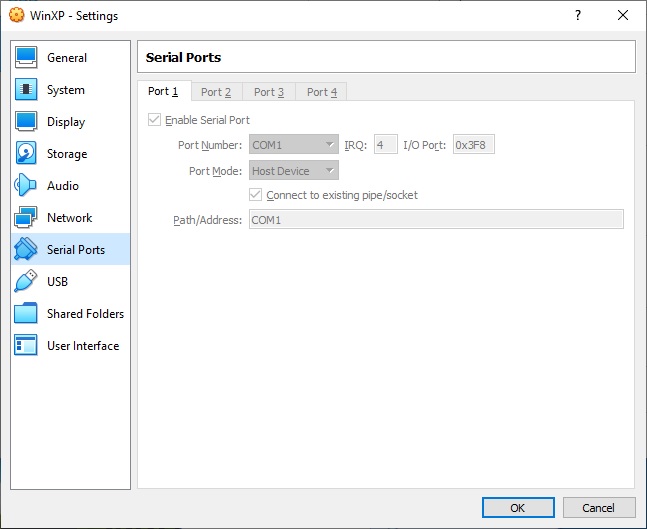
As you can see I’ve simply mapped COM1 on the guest to COM1 on the host, simples !
Copying Motorola CPS into Windows XP
So for the grand finale we can install the Motorola CPS software within Windows XP. How one gets the software installed can be done a few different ways.
I decided to use the VirtualBox shared folders mechanism. With the guest additions installed I found once I’d configured the shared folders they were automatically mapped as a network drive the next time I restarted the Windows XP guest. It was a simple matter to then double click the executable and install.
There were a few websites with rough instructions, but I found after watching the following YouTube video from Peter Downie I was able to get it working in short order;
The other method I’ve used to pass software through to a guest is to use a USB thumb drive. Copy the files from the host to the USB, pass the USB through to the guest, move the files and eject to pass it back. Both methods work just as well as each other.
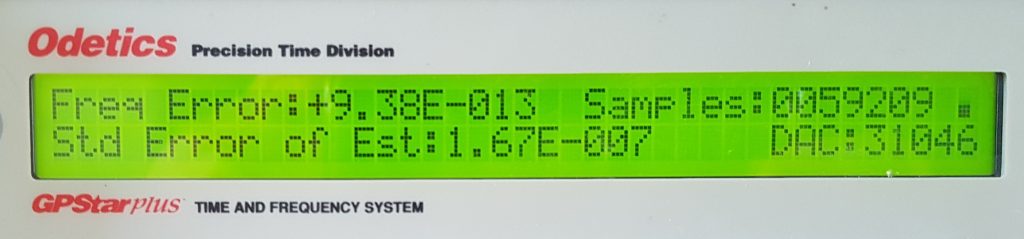
The Proof is in the Pudding
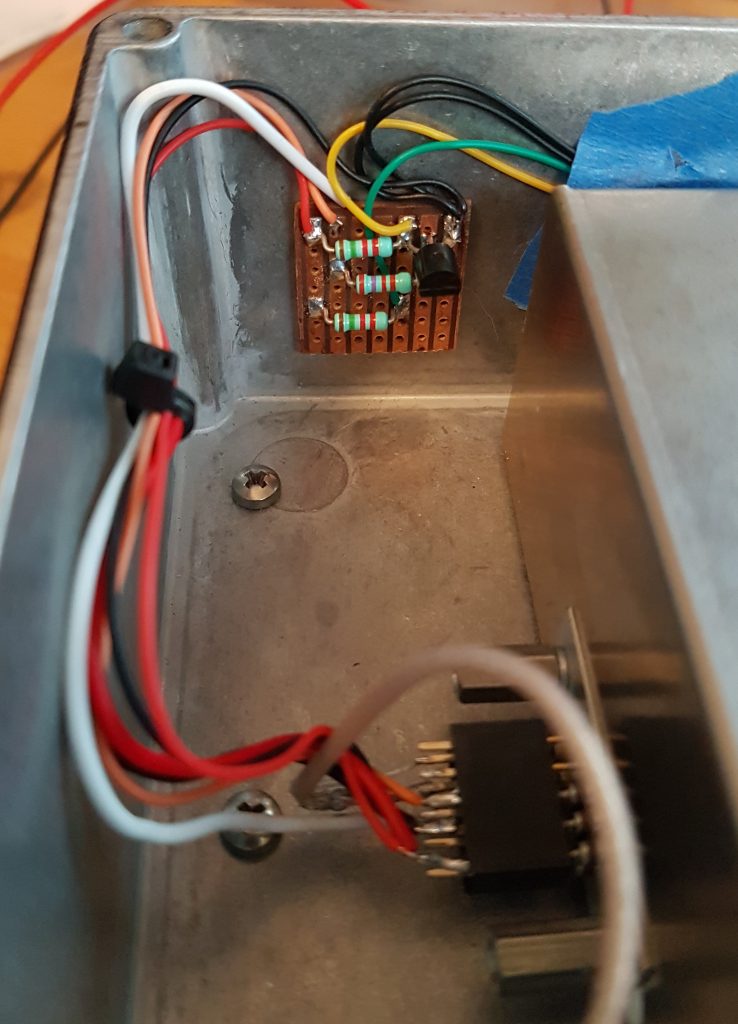
So once you can copy the relevant files into the VM, then it’s a simple matter to install and run the Motorola CPS software. Then simply configure it to talk to the serial port you’ve passed through which is COM1 in my case, then try to read a physical radio. Please note that Motorola CPS software is licensed and cost real $$$ to purchase, please do not request copies of said software fro me as refusal often offends.
You will know you’ve got it right when you hear the radio beep, it says PRGM on the radio display and you are greeted with the contents of your code plug.
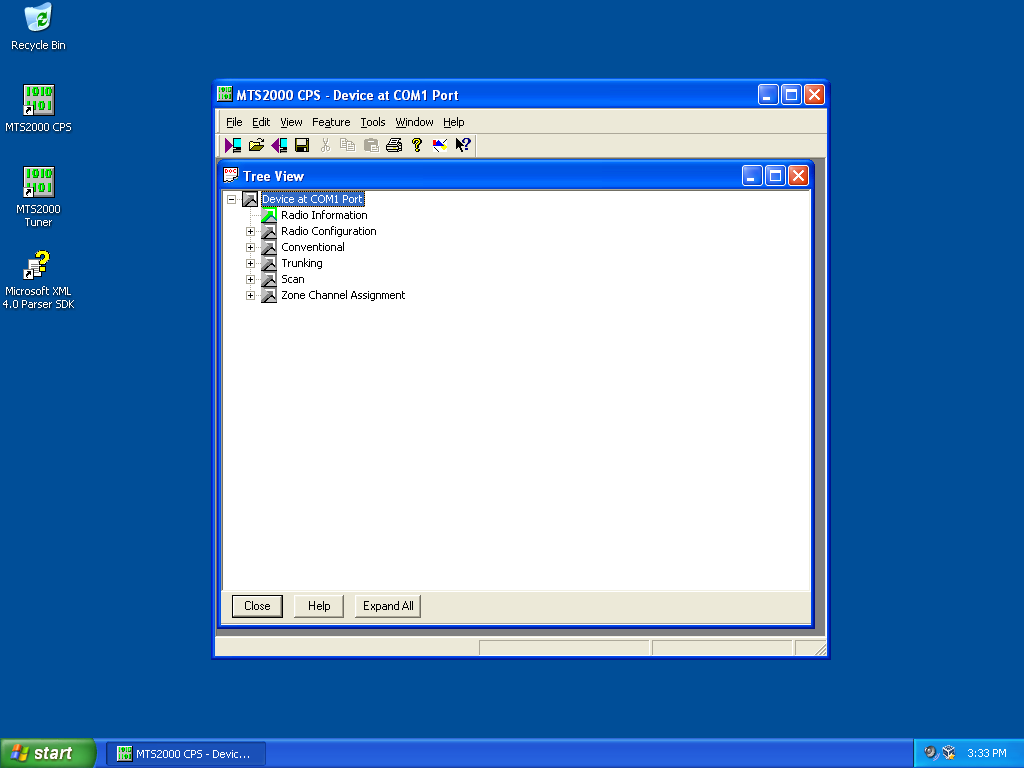
I was certainly relieved to be greeted with the screen shown above, make my changes and write the config back to the radio. I’m once again in business. I hope that other users of older Motorola CPS software find this useful.